D
Dan Goodin
Guest
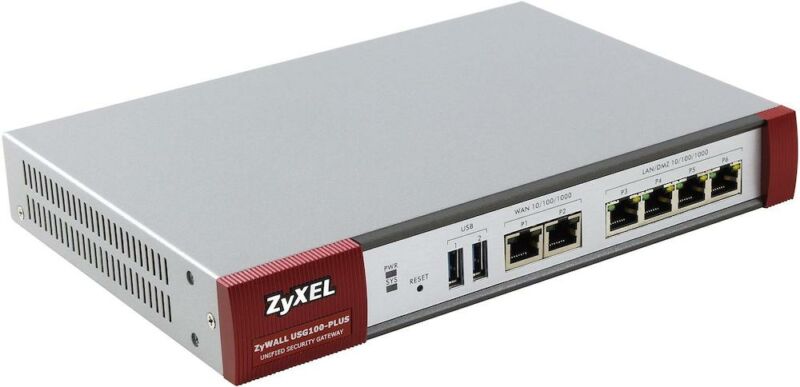
Network device maker Zyxel is warning customers of active and ongoing attacks that are targeting a range of the company’s firewalls and other types of security appliances.
In an email, the company said that targeted devices included security appliances that have remote management or SSL VPN enabled, namely in the USG/ZyWALL, USG FLEX, ATP, and VPN series running on-premise ZLD firmware. The language in the email is terse, but it appears to say that the attacks target devices that are exposed to the Internet. When the attackers succeed in accessing the device, the email further appears to say, they are then able to connect to previously unknown accounts hardwired into the devices.
Continue reading on ArsTechnica
Last edited by a moderator:

