I experience several mysterius events looking into my system.log:
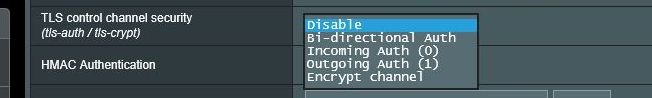
Several failure regarding ovpn-server and suspisious websites errors with TLS. Checking with whois most of them seems bad like this: ovpn-server1[xxxxx]: 167.248.133.140:19808 TLS Error: TLS key negotiation failed to occur within 60 seconds
More ovpn-server - error code 111.
Ovpn-server: WARNING: POTENTIALLY DANGEROUS OPTION --verify-client-cert none|optional may accept clients which do not present a certificate
syslog: PLUGIN AUTH-PAM: BACKGROUND: initialization succeeded. What is this?
kernel: HTB: quantum of class 10001 is big. Consider r2q change. What is this - action?
kernel: SKIPPED false Type 2 Radar Detection. 2, 3, 5 and others. What is this?
All this happen in the night when nobody have been active on my net. Nobody else have been using the openvpn either.
Need help!
Several failure regarding ovpn-server and suspisious websites errors with TLS. Checking with whois most of them seems bad like this: ovpn-server1[xxxxx]: 167.248.133.140:19808 TLS Error: TLS key negotiation failed to occur within 60 seconds
More ovpn-server - error code 111.
Ovpn-server: WARNING: POTENTIALLY DANGEROUS OPTION --verify-client-cert none|optional may accept clients which do not present a certificate
syslog: PLUGIN AUTH-PAM: BACKGROUND: initialization succeeded. What is this?
kernel: HTB: quantum of class 10001 is big. Consider r2q change. What is this - action?
kernel: SKIPPED false Type 2 Radar Detection. 2, 3, 5 and others. What is this?
All this happen in the night when nobody have been active on my net. Nobody else have been using the openvpn either.
Need help!