I know the firewall has inbound filtering, however, I don't see the capability to further custom lockdown the firewall.
Does anyone know how to setup custom outbound rules using the Network Services Filter ?
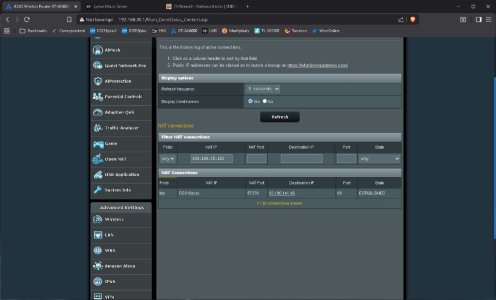
At the bottom of the image below, you have Source IP and Destination IP listed. (ie. 192.168.0.2 - 192.168.0.254)
I'd like to specify an IP range in the box. I already know how to specify a port range.

Does anyone know how to setup custom outbound rules using the Network Services Filter ?
At the bottom of the image below, you have Source IP and Destination IP listed. (ie. 192.168.0.2 - 192.168.0.254)
I'd like to specify an IP range in the box. I already know how to specify a port range.