I just spent 2hrs with AI, couldnt get it to work.
Try this. Maybe my AI is better than your AI...  . Commands below for ease of copy paste, but please read the instructions.
. Commands below for ease of copy paste, but please read the instructions.
As regards getting the RSSI values, I have a script which does that by leveraging the individual scripts (which do that) on each node.
You can DM for a copy but you can probably get your AI to write it for your system, using vibe-coding.
All Commands are issued from MAIN (SSH using e.g. Putty)
For all edits to files I use WinSCP and open the file directly in the dir by double-clicking it.
Step 1: Generate the security keys
Can skip if id_dropbear already exists in /jffs/.ssh
Code:
dropbearkey -t rsa -f /jffs/.ssh/id_dropbear
On modern FW, this should generate both id_dropbear AND id_dropbear.pub files.
It also prints out the full key on the SSH terminal (Putty) screen, along with a "Fingerprint:" line (which is NOT part of the key).
The full key starts with "ssh-rsa" and ends with "YourUserName@YourRouterName".
You can save it to a text file at this point (you can still retrieve it later from the file though).
For completeness, note that older FW with much older dropbear versions only save the private key.
If id_dropbear.pub was NOT created automatically, simply run this second line to extract it:
Code:
dropbearkey -y -f /jffs/.ssh/id_dropbear | grep "^ssh-rsa" > /jffs/.ssh/id_dropbear.pub
Step 2: Add the public key (that you saved above) to Main via the WebGUI (refer attachment)
Main GUI → Administration → System → Authorized Keys field; click Apply.
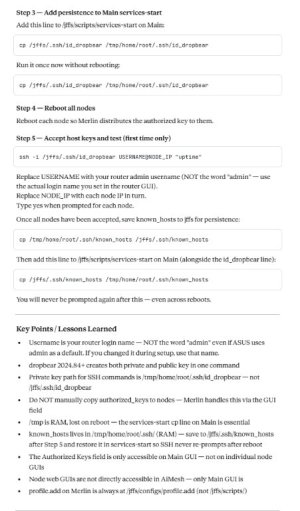
Step 3: Add this line to the /jffs/scripts/services-start file on Main
Code:
cp /jffs/.ssh/id_dropbear /tmp/home/root/.ssh/id_dropbear
Step 4: Reboot
Reboot Nodes (only, NOT Main)
Step 5: Create known host file and make persistent
Issue these one at a time; answer 'y' as a one-off:
Code:
ssh -i /tmp/home/root/.ssh/id_dropbear USERNAME@Node1_IP "uptime"
ssh -i /tmp/home/root/.ssh/id_dropbear USERNAME@Node2_IP "uptime"
ssh -i /tmp/home/root/.ssh/id_dropbear USERNAME@Node3_IP "uptime"
etc...
Once all nodes have been accepted (y), save the generated (normally temporary) "known_hosts" to jffs for persistence over reboots:
If you use WinSCP, you may have to click refresh to check the known_hosts file is actually in /jffs/.ssh
Code:
cp /tmp/home/root/.ssh/known_hosts /jffs/.ssh/known_hosts
Then add this line to /jffs/scripts/services-start on Main (below the id_dropbear line you added in step 3):
Code:
cp /jffs/.ssh/known_hosts /tmp/home/root/.ssh/known_hosts
You should never be prompted for y/n again after this step - even across reboots.
====================================================================
[EDIT1] Refer
post below for background for edit (both keys are generated with one cmd line).
[EDIT2] Refer
this post for persistence.
HTH (and huge thanks to
@rung for the guidance).
k.
p.s. You can retrieve your NodeX_IP in the AiMesh, (select node), Network screen underneath the "Uplink Type" line (amongst other sources).