You "may" be able to track down the process ID on the suspect machine. This will have limited scope of helpfulness but on the suspect Windows machine open a PowerShell window with admin access and paste into prompt:
netstat -ano -p TCP | Where-Object { $_ -match ":22\s+" }
Seems like your SSH listening port is default 22 if not then change the value to your listening port.
The limits are: output works only on existing or recent connections. The PID will display only if the process is still loaded.
Suggest to reboot machine and run immediately as you said it attempts port 22 connection during bootup. Maybe it will help you track down the process in task manager, maybe it won't. I believe you have only about 1 minute for TIME_WAIT entries to see anything at all in netstat.
In this example SSH client connects and you can see it's process ID but mine is configured to exit on disconnect so you also see a TIME_WAIT (recent connection) with no PID value. In this case, it would not be so helpful.
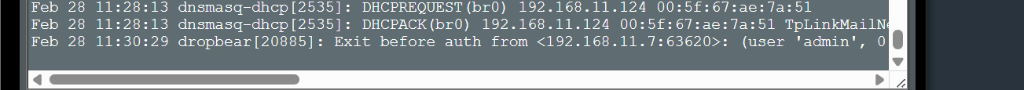
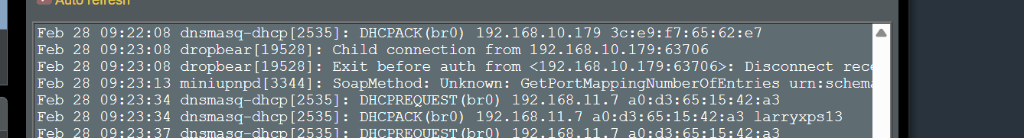
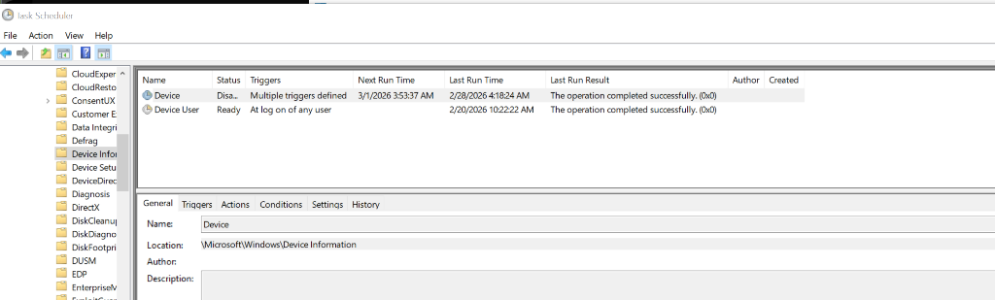
Also suggest reviewing logs that match the timestamp.
May be a good time to review your security practices regarding SSH. Use custom port, disable password logins (use SSH keys only) and absolutely disable WAN access to the service.