VPN Killswitch doesn't not work on RT-AC68U 386.12_4 when the VPN disconnects it still allows client to go over internet exposing local IP. Here are the settings:
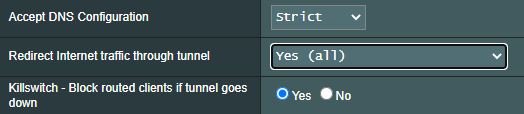
Accept DNS Configuration: Strict
Redirect Internet traffic through tunnel: Yes (all)
Killswitch - Block routed clients if tunnel goes down: Yes
Not sure if its a bug? I have tried using VPN Director policy rule but that didn't help either. Any suggestions?
Accept DNS Configuration: Strict
Redirect Internet traffic through tunnel: Yes (all)
Killswitch - Block routed clients if tunnel goes down: Yes
Not sure if its a bug? I have tried using VPN Director policy rule but that didn't help either. Any suggestions?