I now have the system fully functional - thank you
@Xentrk for all the help, links and pointers provided over the last several days.
- This is what I wanted to achieve:
1. Have the SmartTVs pick up a shared VPN IP through the OVPN Client 1
2. Stream
local Netflix and Prime on the SmartTVs through the WLAN (interface 0)
3. All the other devices on the network use WLAN directly for streaming and are selectively routed through OVPN Client 2 (on another shared VPN IP) to skysports.com.
- This is how it works for me:
- Configured and tested the 2 OVPN Clients for the desired destinations
- OVPN 1 has Policy Rules (strict) selected and blocks routed clients if the tunnel goes down; the 2 SmartTV reserved IPs and the WLAN are defined in the Rules for routing client traffic
- OVPN 2 has Policy Rules enabled and no defined clients; also it doesn't block routed clients if the tunnel goes down
- now for the time consuming part - the dnsmasq and ASN based rules come from all the sources
@Xentrk pointed to in previous posts and the GitHub link - i.e. mining the Diversion dnsmasq log or following it in real-time (VPN disabled), the nslookup / whob method of determining AS numbers, the
https://bgp.he.net/ and
https://www.yougetsignal.com/tools/web-sites-on-web-server/ sites etc.
My Internet provider's AS number came up in pretty much every place. However, the whole thing did not come together until I linked its ASN to both, interface 0 and 2 (although both occurrences show the same number of packets and bytes.)
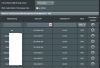
Here is how it all looks like:
Code:
Chain PREROUTING (policy ACCEPT 597K packets, 473M bytes)
num pkts bytes target prot opt in out source destination
1 76057 92M MARK all -- tun11 * 0.0.0.0/0 0.0.0.0/0 MARK xset 0x1/0x7
2 244K 312M MARK all -- tun12 * 0.0.0.0/0 0.0.0.0/0 MARK xset 0x1/0x7
3 2096 170K MARK all -- tun21 * 0.0.0.0/0 0.0.0.0/0 MARK xset 0x1/0x7
4 774K 788M BWDPI_FILTER udp -- eth0 * 0.0.0.0/0 0.0.0.0/0
5 324K 31M MARK all -- br0 * 0.0.0.0/0 0.0.0.0/0 match-set ROGERS.i2_812 dst MARK or 0x2000
6 151K 12M MARK all -- br0 * 0.0.0.0/0 0.0.0.0/0 match-set SkySports_masq dst MARK or 0x2000
7 29874 2847K MARK all -- br0 * 0.0.0.0/0 0.0.0.0/0 match-set SkySports_rev dst MARK or 0x2000
8 324K 31M MARK all -- br0 * 0.0.0.0/0 0.0.0.0/0 match-set ROGERS.i0_812 dst MARK or 0x8000
9 7336 630K MARK all -- br0 * 0.0.0.0/0 0.0.0.0/0 match-set NETFLIX_2906 dst MARK or 0x8000
10 22 2475 MARK all -- br0 * 0.0.0.0/0 0.0.0.0/0 match-set AMAZON_CA dst MARK or 0x8000
11 64587 19M MARK all -- br0 * 0.0.0.0/0 0.0.0.0/0 match-set AMAZON_14618 dst MARK or 0x8000
12 101K 81M MARK all -- br0 * 0.0.0.0/0 0.0.0.0/0 match-set AMAZON_16509 dst MARK or 0x8000
Code:
0: from all lookup local
9990: from all fwmark 0x8000/0x8000 lookup main
9994: from all fwmark 0x2000/0x2000 lookup ovpnc2
10001: from 192.168.1.1 lookup main
10101: from 192.168.1.238 lookup ovpnc1
10102: from 192.168.1.253 lookup ovpnc1
32766: from all lookup main
32767: from all lookup default
Code:
AMAZON_14618 - 188
AMAZON_16509 - 3069
AMAZON_CA - 26
NETFLIX_2906 - 152
ROGERS.i0_812 - 574
ROGERS.i2_812 - 574
SkySports_masq - 394
SkySports_rev - 7