I think you are mixed up. ASDM is monitoring software and ASM is firewall software.GUI or CLI on Cisco still does the same thing. We're beating a dead horse here again. It doesn't matter because it's still the same crap. You can use ASDM on any security device Cisco offers. Just need to DL and put it on the flash to run it.
Enterprise vs SP is also a big difference in the types of equipment being deployed. I've run DC equipment SP equipment SMB equipment.... It's all the same just different price points. If you've touched one Cisco you've touched them all. Physically they're all different in size and capabilities but, they all run the same.
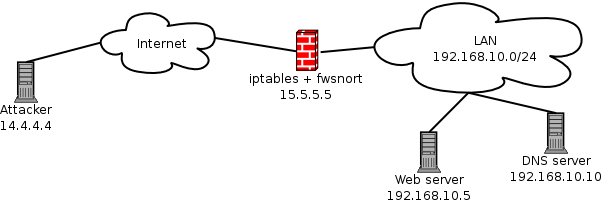
IDS/IPS is all marketing in my book. If you properly configure your rules you don't need either of them nor benefit from the bottlenecks they create. If you're worried about the crap they might alert you about then your IT policies are lacking on the prevention in the first place and you didn't lock things down properly to prevent users from introducing things to the network.
When you properly segregate the networks from each other so they can't cross communicate with each other directly it's not an issue.
40GE is nothing when it's actually 20x20. When you're used to running 100GE 100x100 and the transceiver alone is the size of the phone in your pocket you have something to worry about.
There is a reason people pay 30 to hundred thousand dollars for one piece of Cisco enterprise hardware. I have used both. Cisco small business is not Cisco enterprise equipment. There is a difference.
IDS/IPS is not marketing. It really works. That is why it is so widely used. If it was all crap then it would not be used and it would not cost more. When you get to enterprise level it costs a lot. You can say what you will there is no way a Linux NAT box is going to replace a firewall at a large site, only at home sites like your home. I would not try to run one at my house. And besides I would like a little more than NAT. NAT can be done by a lot of consumer routers. No reason to do it from scratch on a Linux box unless you are having fun.
And I am not sure what you mean by this statement "When you properly segregate the networks from each other so they can't cross communicate with each other directly it's not an issue." In large networks the switches handle all the local network traffic, not firewalls or routers. So this statement makes no sense to me.
I think in large networks the only reason to run a router is if you run something like BGP. The other thing would be you might have one in front of your firewall for VPN connections. It depends on your firewall choice.
Last edited: