A new thread that attempts to pull together all the thoughts on a new home network design. Current set-up is an ASUS RT-AC86U running Merlin with 100/50 WAN connection and a guest Wi-Fi network set-up for IOT devices. We don’t access the network whilst out of the home so don’t run a VPN other than when working from home in which case, I’m using a VPN Client connected to the work VPN Server. My requirements going forward are to
Edit 1. I'm not concerned, at this point, about >1GB WAN connection as this is in our distant future. The idea of 10G switch has an attraction but the value proposition is limited as none of our devices support 10GB and it's rare to push large files around the house other than videos which Plex plus current 1GB LAN seem to handle fine. Let me know if I'm missing the point.
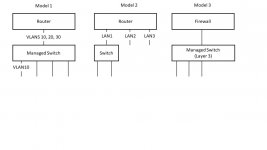
Edit 2 The reason for the separate router and switch (rather than a combined router | switching) is that these are separate tasks that are best done in separate devices. Again if this doesn't make sense then let me know.
- address work requirement to secure work computer from the remainder of the home network (whilst allowing this computer to access specific services on the network, e.g., printer, Roon media)
- address security risks associated with smartphones, laptops that family members use on public Wi-Fi etc. (whilst allowing this computer to access specific services on the network, e.g., printer, Roon media)
- be able to take advantage of a planned infrastructure upgrade that will give a 1GB internet download connection
- simple to configure set-up (concerned that complex config. will result in mistakes and downtime)
- Tweak existing set-up via adding a second router that puts the work computer on an entirely different network and take advantage of another Guest network on the RT-AC86U to host the smartphones, laptops etc. This approach keeps me in the consumer domain which is good, but it won’t be possible for the work computer and family devices to access printers etc which is a major issue. Also, it seems as if 1GB might be problematic with RT-AC86U or a replacement.
- Restructure the network around separate router, switches and access points using VLAN to provide the segmentation. This approach seems like a lot more effort but, potentially, rewarding although I am concerned about my capability to configure (fine to follow instructions and do a bit of problem diagnosis but don’t have the context if things get too complex).
Edit 1. I'm not concerned, at this point, about >1GB WAN connection as this is in our distant future. The idea of 10G switch has an attraction but the value proposition is limited as none of our devices support 10GB and it's rare to push large files around the house other than videos which Plex plus current 1GB LAN seem to handle fine. Let me know if I'm missing the point.
Edit 2 The reason for the separate router and switch (rather than a combined router | switching) is that these are separate tasks that are best done in separate devices. Again if this doesn't make sense then let me know.
Last edited: